I can't stand to see these games being hacked anymore. Sunflower was open source, and with that many people are using its source codes and creating version variations of the games, but it has a major flaw that all of them, or at least (almost all), are being hacked, being stolen from liquidity pool somehow.
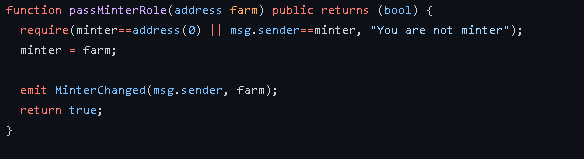
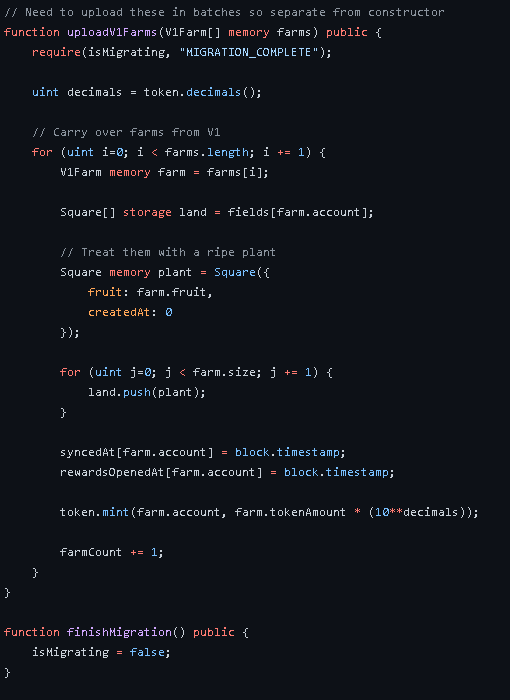
Someone with more experience in blockchain contracts would be able to tell where this flaw is, which allows this hacker to run this exploit.
I will leave below the two wallets that the hacker uses and some of his actions that he performed to steal the liquidity pool.
HFF - 0x36c0845773a6066a25f228e62248915ef481c38c
CFG - 0xa1F8541DF23Cf0F3551BDc665E9Abd31f125Bc37
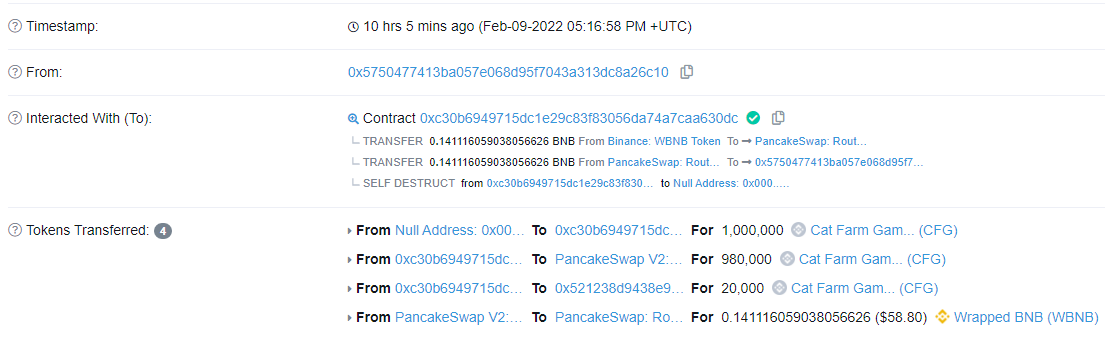
Above are 2 heists on 2 different tokens.
Hacker Address 1: 0x5750477413ba057e068d95f7043a313dc8a26c10
Hacker Address 2: 0x6c9244d2f9febf230f7be9de2d185b330e431261
TxId Hacker 1.1: https://polygonscan.com/tx/0xb4127ff702af9a96ff97c0c01d76f9966984b80cb63fec352e76d611e3120b7e
TxId Hacker 1.2: https://polygonscan.com/tx/0xe0c0621b54cd7cb63bba2fb19913b00d644e3f003608111d7fe00aee6f8cdef6
TxId Hacker 2.1: https://bscscan.com/tx/0x6c4e018f6f427108695f029237828704aec17799020837236fbf46c475efeef4
TxId Hacker 2.2: https://bscscan.com/tx/0xe89a289c56f1477311d1e17189df764cc5791cae6032e0547458a3698f37e909
TxId Hacker 3.1: https://polygonscan.com/tx/0x50cd0dd569d45ac9b286d8deb5b9eb72bd0b8121c7ef524a5d6a2e270af0402e
TxId Hacker 3.2: https://polygonscan.com/tx/0x523ea53d8deaa0a726825739e0bf4e81a1c9c83b45cfd8000fe4d22a3663c8cd
I will list below all the versions that I know of and if they were stolen or not.
SUNFLOWER - POLYGON - (ORIGINAL) (NOT HACKED)
TOKEN: 0xdf9b4b57865b403e08c85568442f95c26b7896b0
FRUIT FARM - BSC - (NOT HACKED)
TOKEN: 0xa2e05fee995d84e388111065f9da0e1fd0358a0b
MY LITTLE FARM - POLYGON - (HACKED)
TOKEN: 0xed2f85f446281a31bcae074938e867422f5074c8
FISHLAND - POLYGON - (HACKED)
TOKEN: 0x1816a91ee2e30aa39dee4fd24590faf0087b5a6c
CAT FARM - BSC - (HACKED)
TOKEN: 0xa1F8541DF23Cf0F3551BDc665E9Abd31f125Bc37
HERO FARM - POLYGON - (HACKED)
TOKEN: 0x36c0845773a6066a25f228e62248915ef481c38c
MOONFLOWER - AURORA - (HACKED)
TOKEN: 0x1103f33c4aa272dd3fdd73724f492ee35f097644
CRYPTO FARM TOWN - AURORA - (HACKED)
TOKEN: 0x330db1dd6d150727eeb53feaf5d485bce2aa326f
The only copy that was not hacked was Fruit Farm.
What do you have to do to correct this huge flaw?
Copies have been appearing all over the world, and we need someone who can fix it, because we know it won't stop being released, and that only has to denigrate the image of "crypto", "blockchain", "NFT". With that, fewer people can come to this market, and we can't let this hacker get away with taking liquidity out of these contracts.
Anyone who knows how to fix this problem, let's try to publicize this fix so that people can stop losing money, because many enter these projects, and most of them lose, and yet they think it was rug pull, further staining our nft market .